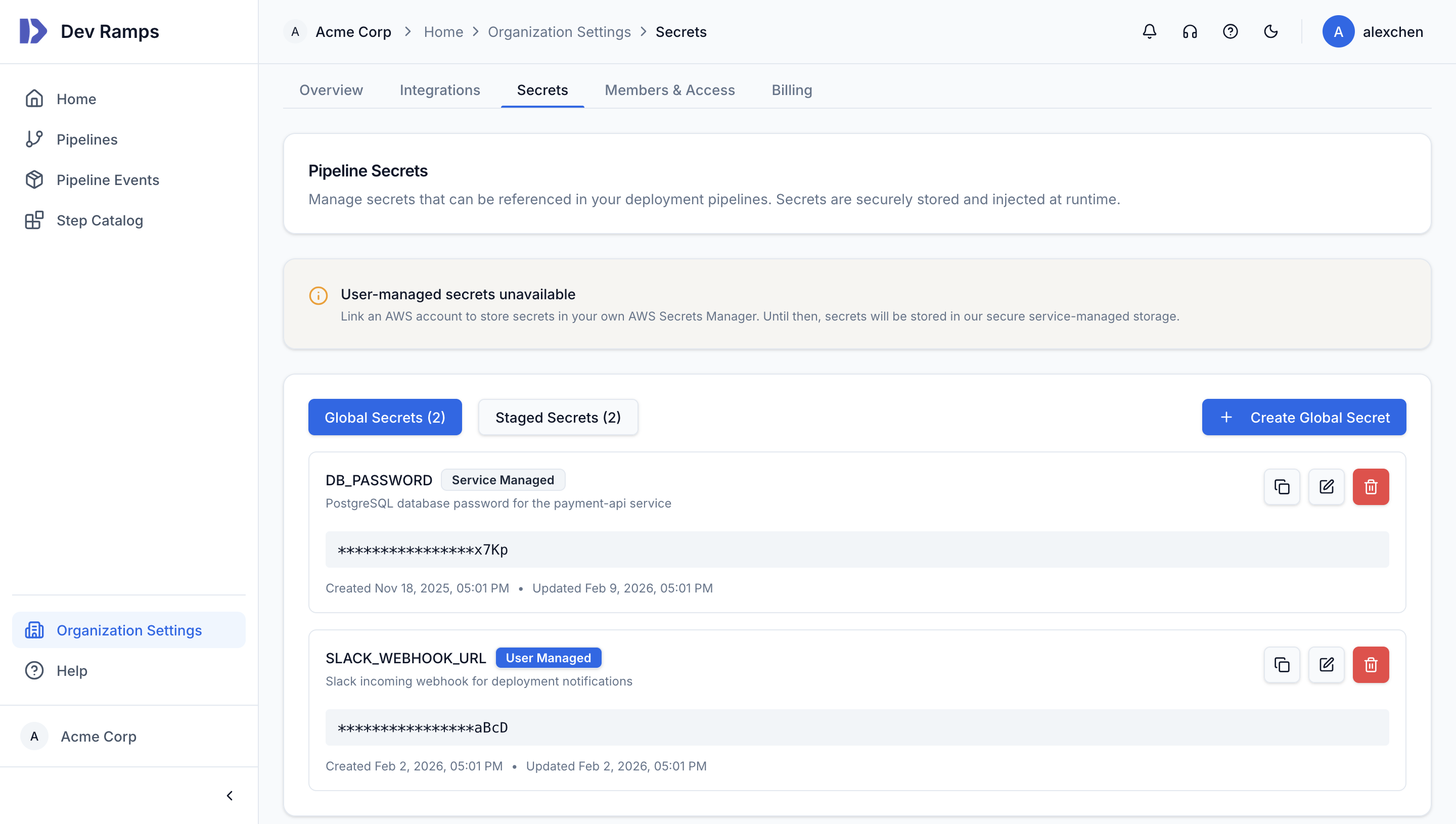
Secrets Management
Secrets are stored in AWS Secrets Manager within your accounts and injected into services at runtime. Dev Ramps never sees or stores your secrets—they stay in your AWS environment.
AWS Secrets Manager
All secrets are stored in AWS Secrets Manager with encryption at rest using KMS keys you control.
Automatic Rotation
Configure automatic rotation for database credentials and API keys. Dev Ramps handles rotation without downtime.
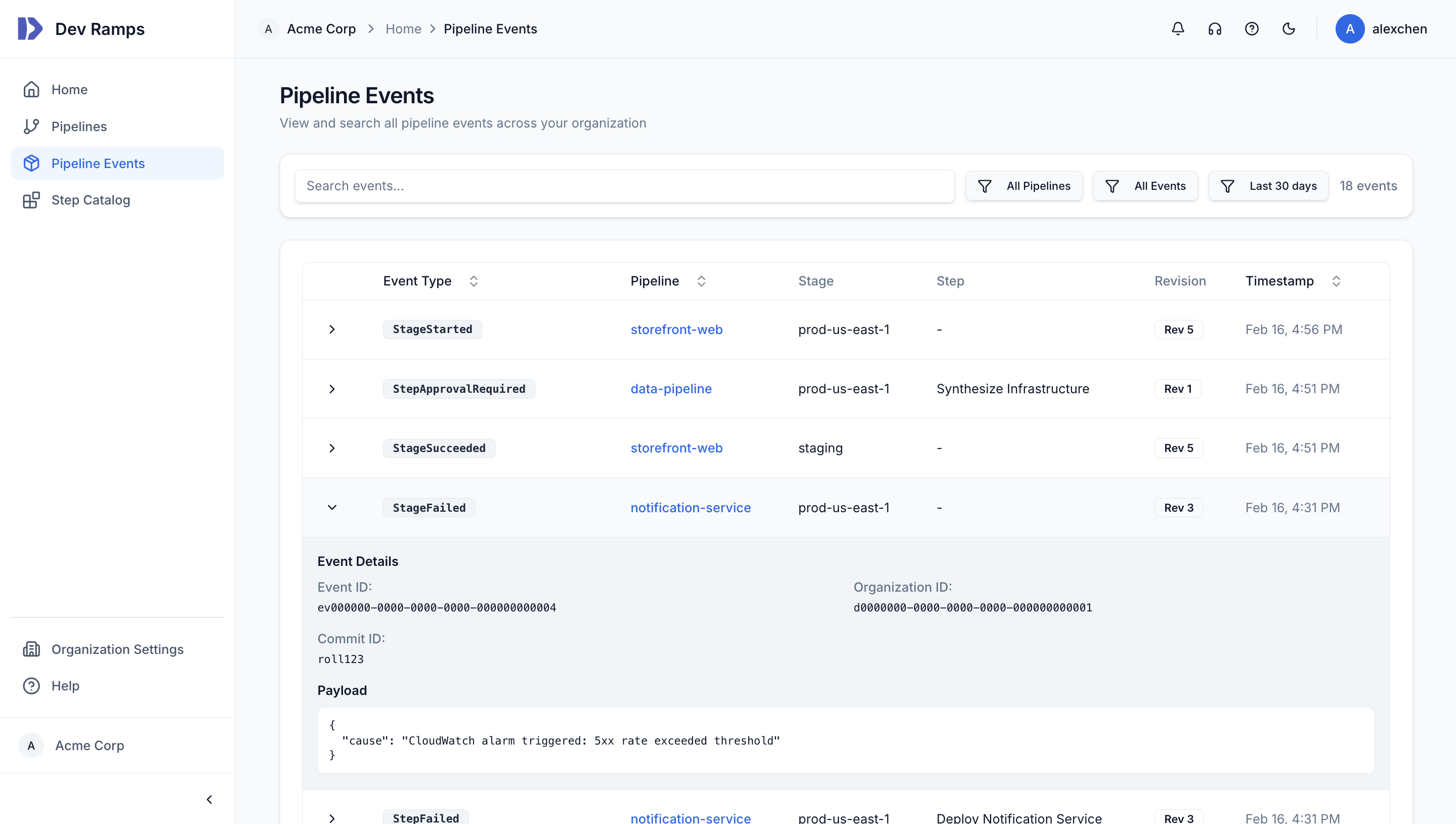
Audit Trail
All secret access is logged via CloudTrail. Know exactly when and how secrets are accessed.
No Plaintext Secrets
Secrets are never stored in environment variables, config files, or logs. Injected at runtime via secure channels only.