Why Dev Ramps
Production-ready infrastructure, without the platform team overhead
Fast Path to Production
Declarative CI/CD instead of scripts
Replace deploy scripts, Makefiles, and GitHub Actions workflows with a single YAML file. Define what you want — Dev Ramps handles how.
See how it works →aws ecs update-service \
--force-new-deploy || exit 1
COPY . /app
RUN npm ci && npm run build
deploy:
runs-on: ubuntu-latest
steps: # ...187 lines
./scripts/deploy.sh staging
deploy-prod:
./scripts/deploy.sh prod
# TODO: fix health check
desired_count = var.count
build:
commands:
- ./scripts/build.sh
# CAREFUL: run manually
PREV_TAG=$(git log ...)
cloud_provider: AWS
stages:
- name: staging
- name: production
steps:
- type: DEVRAMPS:ECS:DEPLOY
- type: DEVRAMPS:APPROVAL:BAKE
# rollbacks, bake, approvals — built in
AWS-Native
Connect your AWS accounts in minutes
One CLI command bootstraps least-privilege IAM roles across your AWS accounts. No manual CloudFormation, no credential management.
See how it works →Production Safety
Enterprise safety mechanisms, zero setup
Rollbacks, bake times, deployment time windows, and CloudWatch alarm-triggered auto-rollback — all built in, zero setup.
See how it works →Pipeline Health Metrics
See exactly where your pipelines are slowing down
P50 deploy time, % time blocked, inventory age — see which pipelines slow your team down and identify bottlenecks before they become problems.
See how it works →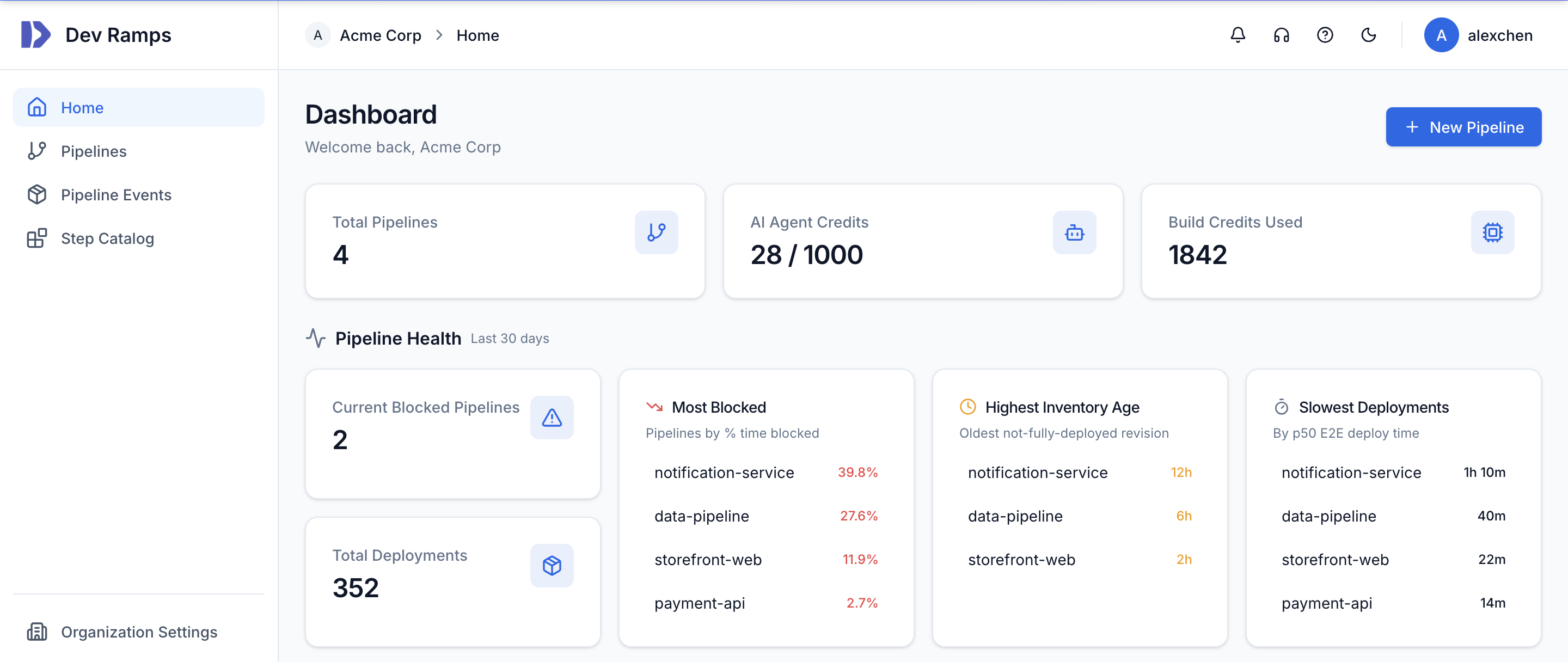
AI Agent Integration
The first CI/CD platform built for AI coding agents
AI coding agents claim ephemeral environments, deploy, verify, and iterate — all through a standard tool interface. Real infrastructure, not mocks.
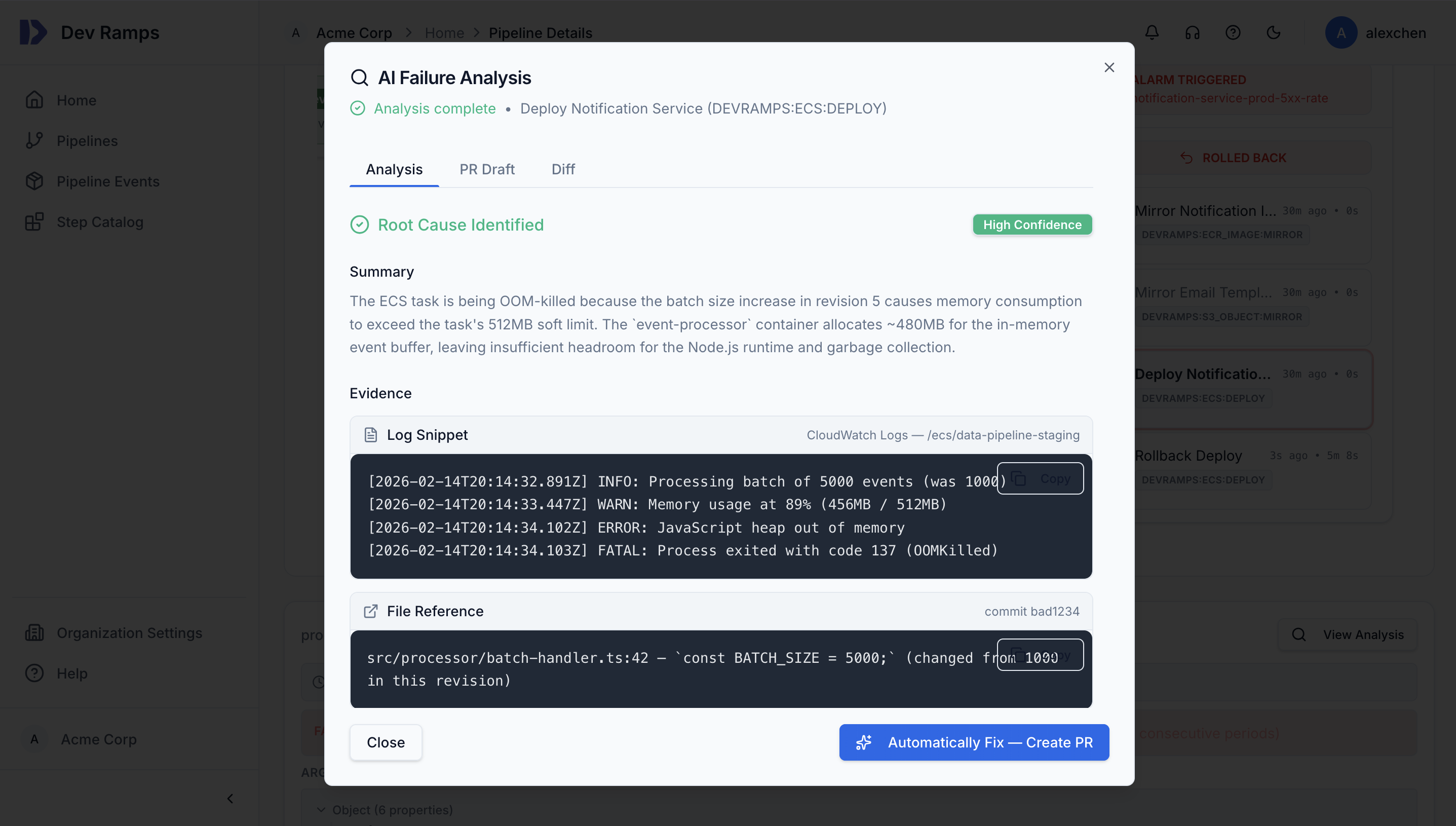
See how it works →AI-Powered Reliability
AI that diagnoses and fixes pipeline failures
When a deployment fails, Dev Ramps AI reads your logs and source code, identifies the root cause, and can auto-generate a fix PR. Reduce pipeline toil and unblock developers faster.
- Automatic root cause analysis on failure
- AI-generated fix PRs to unblock your team
- Context-aware analysis across logs and source code